Security Implementation Diagrams for Azure Synapse Analytics¶
Home > Diagrams > Security Diagrams
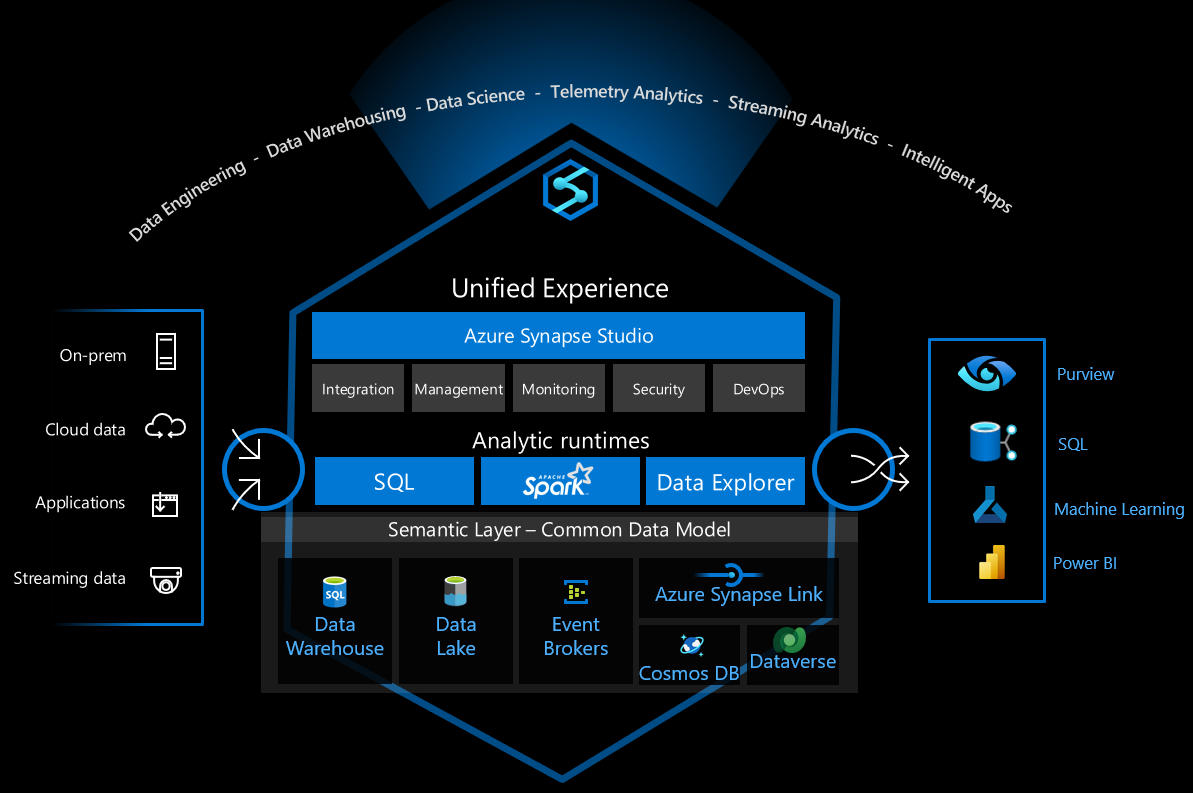
This section provides security implementation diagrams for Azure Synapse Analytics, focusing on security patterns and best practices.
Defense-in-Depth Security Architecture¶
This diagram illustrates the defense-in-depth security model for Azure Synapse Analytics.

Network Isolation Architecture¶
This diagram shows the network isolation architecture for securing Azure Synapse Analytics workspaces.
Data Protection Security Model¶
This diagram illustrates the comprehensive data protection model for Azure Synapse Analytics.
Identity and Access Management Architecture¶
This diagram depicts the identity and access management architecture for Azure Synapse Analytics.
Sensitive Data Protection Framework¶
This diagram shows the sensitive data protection framework for Azure Synapse Analytics.
Compliance Controls Architecture¶
This diagram illustrates how Azure Synapse Analytics implements controls for various compliance standards.
Security Implementation Best Practices¶
When implementing security for Azure Synapse Analytics, follow these best practices:
- Network Security
- Implement private endpoints for all Synapse components
- Use network security groups to restrict traffic
- Deploy Azure Firewall for advanced threat protection
-
Utilize virtual network service endpoints for Azure services
-
Data Protection
- Enable transparent data encryption for all data at rest
- Implement customer-managed keys with Azure Key Vault rotation
- Apply column-level encryption for sensitive data
-
Use dynamic data masking for PII data
-
Identity and Access Management
- Implement Azure AD authentication for all access
- Use conditional access policies for sensitive workloads
- Apply least privilege principle with custom RBAC roles
-
Implement managed identities for service-to-service authentication
-
Monitoring and Compliance
- Enable diagnostic logs for all Synapse components
- Implement advanced threat protection for SQL pools
- Create custom alerts for security events
- Perform regular vulnerability assessments



