Private Link Architecture¶
Home > Architecture > Private Link Architecture
Overview
This guide details the architecture patterns for implementing Azure Private Link with Azure Synapse Analytics, ensuring secure network isolation and private connectivity.
🔐 Private Link Architecture Components¶
Azure Private Link provides secure private connectivity to Azure Synapse Analytics and related services.
-
🔗 Private Endpoints
The interface for connecting privately to Azure services
-
🌐 DNS Configuration
Private DNS integration for name resolution
-
📡 Network Topology
VNet design for Synapse with Private Link
-
✅ Connectivity Validation
Testing and validating private connectivity
Reference Architecture¶
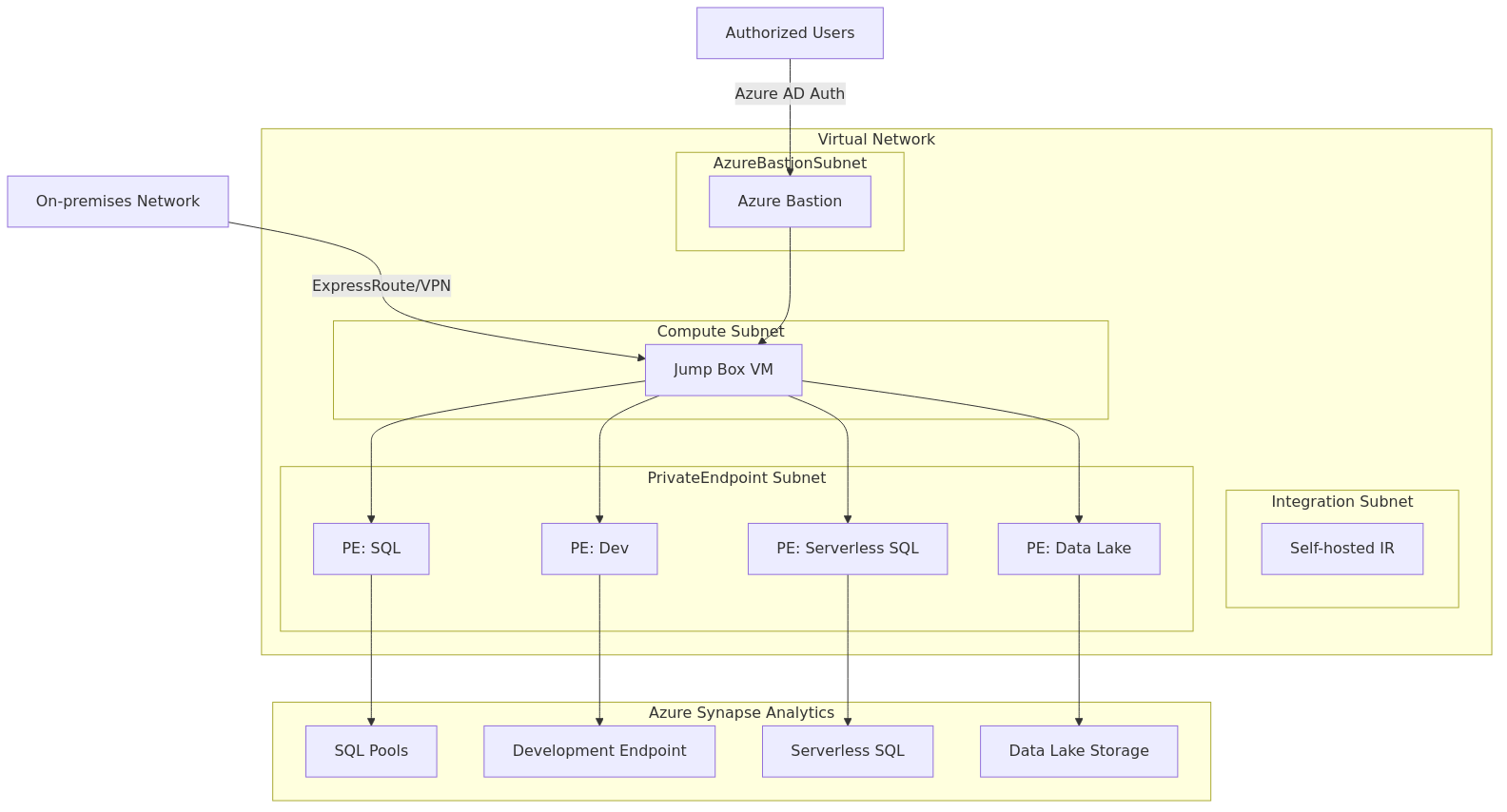
Private Endpoint Design¶
Security Alert
Each Synapse component requires its own private endpoint with the correct group ID to function properly.
Azure Synapse Analytics requires multiple private endpoints for complete private connectivity:
| Component | Group ID | DNS Zone | Purpose |
|---|---|---|---|
| SQL | Sql | privatelink.sql.azuresynapse.net | SQL pools access |
| SQL On-Demand | SqlOnDemand | privatelink.sql.azuresynapse.net | Serverless SQL access |
| Dev | Dev | privatelink.dev.azuresynapse.net | Development experience |
| Web | Web | privatelink.azuresynapse.net | Web UI access |
ARM Template for Private Endpoints
{
"type": "Microsoft.Network/privateEndpoints",
"apiVersion": "2020-11-01",
"name": "synapse-sql-endpoint",
"location": "[parameters('location')]",
"properties": {
"privateLinkServiceConnections": [
{
"name": "synapse-sql-endpoint",
"properties": {
"privateLinkServiceId": "[resourceId('Microsoft.Synapse/workspaces', parameters('workspaceName'))]",
"groupIds": [
"Sql"
]
}
}
],
"subnet": {
"id": "[variables('subnetId')]"
}
},
"dependsOn": [
"[resourceId('Microsoft.Synapse/workspaces', parameters('workspaceName'))]"
]
}
Private DNS Configuration¶
Each private endpoint requires corresponding DNS zone configuration:
- Create private DNS zones for each endpoint type
- Link DNS zones to your virtual network
- Create A records for each private endpoint
- Configure DNS resolution between on-premises and Azure
# Example: Create Private DNS Zones
$resourceGroup = "myResourceGroup"
$vnetName = "myVNet"
$vnetId = (Get-AzVirtualNetwork -Name $vnetName -ResourceGroupName $resourceGroup).Id
# Create DNS zones
New-AzPrivateDnsZone -ResourceGroupName $resourceGroup -Name "privatelink.sql.azuresynapse.net"
New-AzPrivateDnsZone -ResourceGroupName $resourceGroup -Name "privatelink.dev.azuresynapse.net"
New-AzPrivateDnsZone -ResourceGroupName $resourceGroup -Name "privatelink.azuresynapse.net"
# Link DNS zones to VNet
New-AzPrivateDnsVirtualNetworkLink -ResourceGroupName $resourceGroup `
-ZoneName "privatelink.sql.azuresynapse.net" `
-Name "link-to-$vnetName" `
-VirtualNetworkId $vnetId `
-EnableRegistration $false
# Repeat for other DNS zones
Network Topology¶
Implement these network topology best practices:
- Hub-Spoke Model - Central connectivity hub with Synapse in a spoke VNet
- Dedicated Subnets - Separate subnet for private endpoints
- Network Security Groups - Control traffic flow between subnets
- Route Tables - Direct traffic through security appliances when needed
- Azure Firewall - Filter outbound traffic from Synapse
Best Practice
Use subnet segregation to separate private endpoints by service type for better security and management.
Connectivity Validation¶
Validate your private link configuration with these methods:
- DNS Resolution Testing:
# Test DNS resolution
nslookup myworkspace.sql.azuresynapse.net
# Should resolve to private IP address
- Connection Testing:
- Network Path Analysis:
Hybrid Connectivity Scenarios¶
Integration Point
ExpressRoute or Site-to-Site VPN integration is essential for on-premises to Azure Synapse private connectivity.
Configure these hybrid connectivity patterns:
- ExpressRoute with Private Peering - Dedicated circuit for low-latency connectivity
- Site-to-Site VPN - Encrypted connection over the internet
- Point-to-Site VPN - For individual client connections
- DNS Forwarding - Configure DNS forwarding for on-premises name resolution
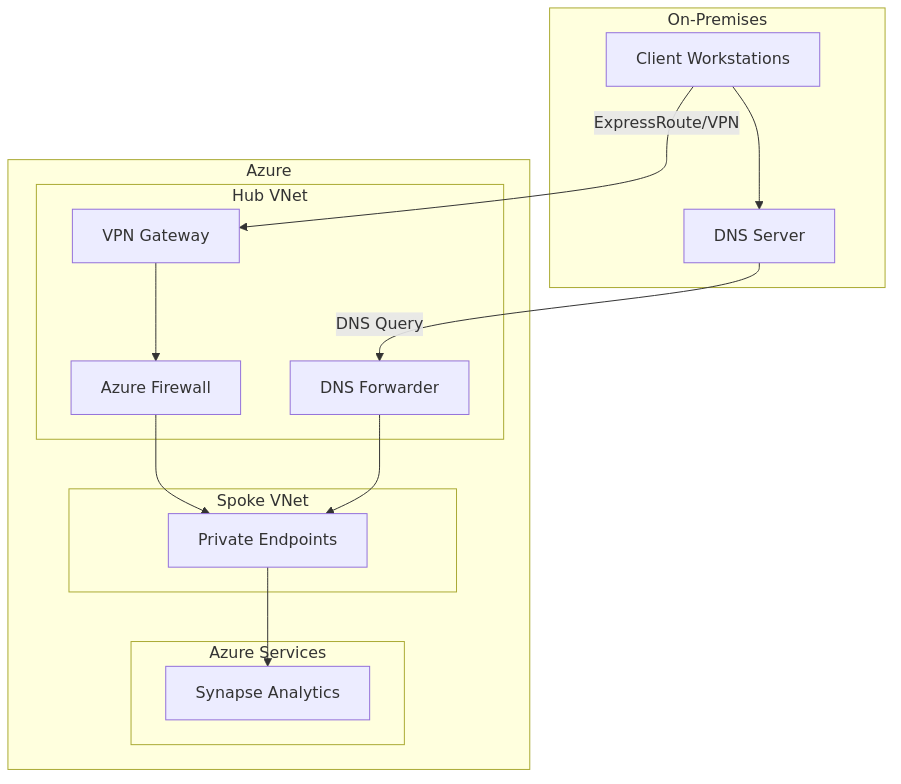
Scalability and High Availability¶
Design your private link architecture for scalability and high availability:
- Multiple Private Endpoints in different subnets for load distribution
- Redundant ExpressRoute Circuits for hybrid connectivity
- Zone-Redundant VPN Gateways for high availability
- Multiple DNS Servers for resilient name resolution
- Cross-Region Private Endpoints for disaster recovery scenarios
Implementation Checklist¶
- Create virtual network with dedicated subnet for private endpoints
- Create private endpoints for all Synapse components (SQL, Dev, Web, etc.)
- Configure private DNS zones and link to your virtual network
- Set up DNS resolution between on-premises and Azure
- Configure NSGs with appropriate security rules
- Implement hybrid connectivity (ExpressRoute or VPN)
- Test connectivity from all required client locations
- Document network architecture and DNS configuration
